How to Report a Security Incident to Internal Stakeholders
The need to respond quickly and to communicate on a real-time basis after an organization has been hit by a cyber attack is very critical.
Just as important is the need to communicate after the cyber-attack has been specifically identified and its impact has been resolved.
After all, people will want to know what exactly has happened, the damages and/or losses it has created, and what can and will be done in the future to prevent it and similar attacks from occurring.
In these instances, it is imperative to communicate all of this to parties that are both internal to the business or corporation (such as the employees, executives, board of directors, investors – these are considered to the “internal stakeholders”) as well as external (such as the partners, clients, suppliers, distributors, etc. – these are considered to the “external stakeholders”).
Thus, withholding any kind of information about the cyber attack could lead to a serious level of mistrust and misunderstandings.
Therefore, the representatives of the Incident Response Team have to open and be forthright as to what exactly happened.
How this information will be disseminated to the internal stakeholders is entirely up to the organization – there is no hard and fast rule for this.
For instance, it could take place as a memo, an e-mail, or it could even be posted on the company intranet.
However, in the end, perhaps having an open forum where the internal stakeholders are physically present could be the best avenue to take.
Taking this approach will allow for a real time questions/answers session to take place, and also the internal stakeholders will feel that their input and suggestions will be valued and taken seriously.
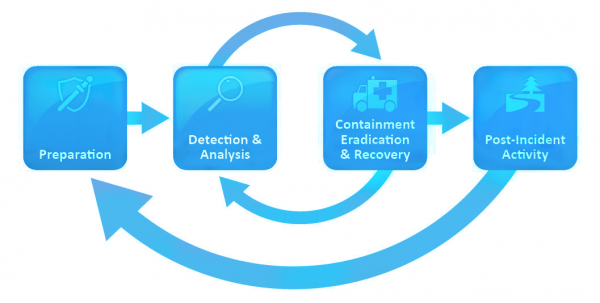
However, in order to decide what will be formally communicated to the internal stakeholders, a defined process must be followed, which is as follows:
1. Triage the Situation:
The three fundamental questions about the cyber-attack must first be answered. These are also known as the four “W’s”:
> Whom specifically launched the cyber-attack?
> Why did the cyber-attack occur (in other words, what was the underlying motive)?
> What parts of the organization did the cyber-attack effect?
> Where was the cyber-attack launched from?
2. Decide the specific medium in which the internal stakeholders will be notified:
As mentioned, this could take place either in a print, electronic, or direct person approach.
However, whatever the decided medium is, it is important that all messages (such as e-mails and texts) be kept within the Incident Response Team until the above questions have been fully answered.
3. Manage the Timing of the Communication:
In this step, the internal stakeholders need to be told the avenue of how they will be informed of the cyber-attack, and when such communications will actually occur.
4. Rehearse the message:
At this stage, it will be important to conduct a dress rehearsal of the actual message that will be communicated among the internal stakeholders.
For example, if it is in a print or electronic form, it will be important that all members of the Incident Response Team review it carefully before it is distributed.
… Or, if it will be open forum based, then the presentation that will be given needs to be practiced, as well as the question/answer session, where it will be important to brainstorm any potential items that could be questioned by the internal stakeholders.
Conclusions
As important as it is to report a cyber-attack to the internal stakeholders after it has happened, the same is true of reporting to the external stakeholders. This will be the focal point of our next blog post of the series.