The Importance of Communications in Incident Response
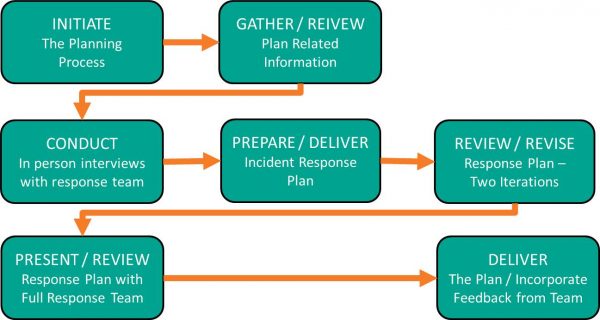
Just as much as it is important to have a clearly defined Incident Response Plan and having the Incident Response team in place, the lines of communication are also equally important.
Responding to a cyber-attack can be chaotic enough, and this does not need to be made worse by not communicating with the members of the Incident Response team in a clear and succinct fashion.
After all, reducing the downtime as much as possible is one of the key goals of Incident Response, and any improper communications can only further exacerbate a tense situation even more.
The importance of Effective Incidence Response communications (also known as the “Crisis Communications Plan”) encompasses three key areas:
1) Communications Internal to the Business or Corporation:
By maintaining open lines of communications, this will help minimize the risk of any sensitive information from being inadvertently released to third parties.
Any unauthorized release of information could impede any subsequent investigation. It will also serve as a vehicle in which to minimize any rumors or speculation.
One of the best methods to have good communications is to ensure that each part of the Incident Response Plan covers how information and data will be relayed. This includes among the team members that are responsible for that specific component of the plan.
For example, the mechanisms that will be used to communicate with each other need to be clearly defined:
> Will there be a central hotline for the team members to call into?
> Will there be a main command center from which all communications will be centralized and then dispersed among the Incident Response Team members?
> What will be the main vehicle(s) of communications-wireless devices, smartphones, etc.? Will each member of the Incident Response Team have a dedicated device for IR communications, or will their current work issued device(s) be sufficient enough?
> What will the form of communication be? For instance, will it be e-mail, actual phone conversations, text messages, instant messages, etc.?
> How often will these lines of communications be tested in order to ensure that they will work quickly and efficiently when they’re needed?
2) Communications for Compliance Related Issues:
After a cyber-attack has occurred, a business or corporation may have to formally report to the federal authorities:
- what exactly has happened,
- the extent of the damage that was caused, and
- which parties were impacted (for instance, customers, suppliers, other 3rd party vendors, etc.).
If there is a time delay or failure to report this, it is quite possible that the organization could face severe financial penalties.
In other words, this aspect of the IR communications process should be a part of the planning process, instead of making it a reactionary one. In this aspect, the legal department from the organization must also be included.
For example, they can assist in determining how the affected parties should be notified, and how exactly the security breach should be communicated. This aspect is very important, so that a violation of any regulatory or privacy requirements does not actually occur.
3) Communications with the Media:
In this aspect, the public relations department needs to be involved in any Incident Response communications.
They can act as a conduit for building up a good rapport with the local and state law enforcement agencies when reporting the occurrence of a cyber-attack. They can also help prepare the proper documents that are needed to relay information to the public such as press releases, announcements, and other forms of disclosure statements.
It is also important to have a member of the IT staff be involved in this part of the IR communications process as well, so that they help break down all of the so called “techno-jargon” into a language that will be easily and clearly understood by the public.
It is important to note that the documents here will not contain each and every aspect of what exactly has transpired. Therefore, it is crucial that the two sides (the designated PR and IT staff members) from the organization work together in a harmonious fashion to help ensure that the information which is communicated to the public is not taken out of context.
The bottom line is that by having effective Incident Response communications, an organization could actually win praise among customers, investors, regulatory agencies, and even the public by being open, honest, and forthright in a timely manner after it has been impacted by a cyber-attack.
In summary, the key benefits of effective Incident Response communications are as follows:
> It will help to increase an overall sense of heightened security awareness among the employees of the organization;
> It can help to mitigate the degree of severity of a cyber-attack;
> It can help reduce the time it takes to respond to a cyber-attack;
> It can help the business entity identify a threat before it actually happens;
> It will help to remind employees of the organization as to what matters most in a crisis situation. For example:
- We care about our investors and customers;
- We are responding to the cyber-attack in a quick and timely fashion;
- We will cooperate with investigative authorities to determine what happened and who did it.
Conclusions
In our next blog post of the series, we will examine how to craft a communications plan that is specific to your business.