Our last blog post of this series reviewed how the process of how Biometrics can be used for Logical Access Entry. Specifically, it examined:
- The Identification Process;
- Logical Access Entry.
In this blog post, we look at two applications that can be used to log into a workstation or your network infrastructure – bypassing the need for a password.
The Biometric Devices That Are Used in Logical Access Entry Applications
For Logical Access Entry applications there are two primary type of Biometric Modalities that are used:
- Fingerprint Recognition;
- Iris Recognition.
Both of these Modalities can either come as standalone devices, or embedded into the computer or wireless device itself.
In the former, these devices are small enough that they can literally either sit on top of the server, or beside it.
They are connected via a simple USB connection.
It’s important to note at this point that the use of Biometrics as a means of Logical Access Entry is also referred to as “Single Sign on Solutions”, or “SSOs” for short.
An example of a USB Connected Fingerprint Recognition device is illustrated below:

The glass that can be seen at the top of the device is actually the Optical Sensor.
This is where the employee can place their fingerprint in order to have it scanned to complete the identification process.
An example of a USB Connected Iris Recognition device is illustrated below:

For this kind of Modality, the employee will have to hold this device a few inches away from their eye.
From there, the circular component (which is an actual camera) will take images of the iris, and convert them over to the raw images so that the unique features can be collected.
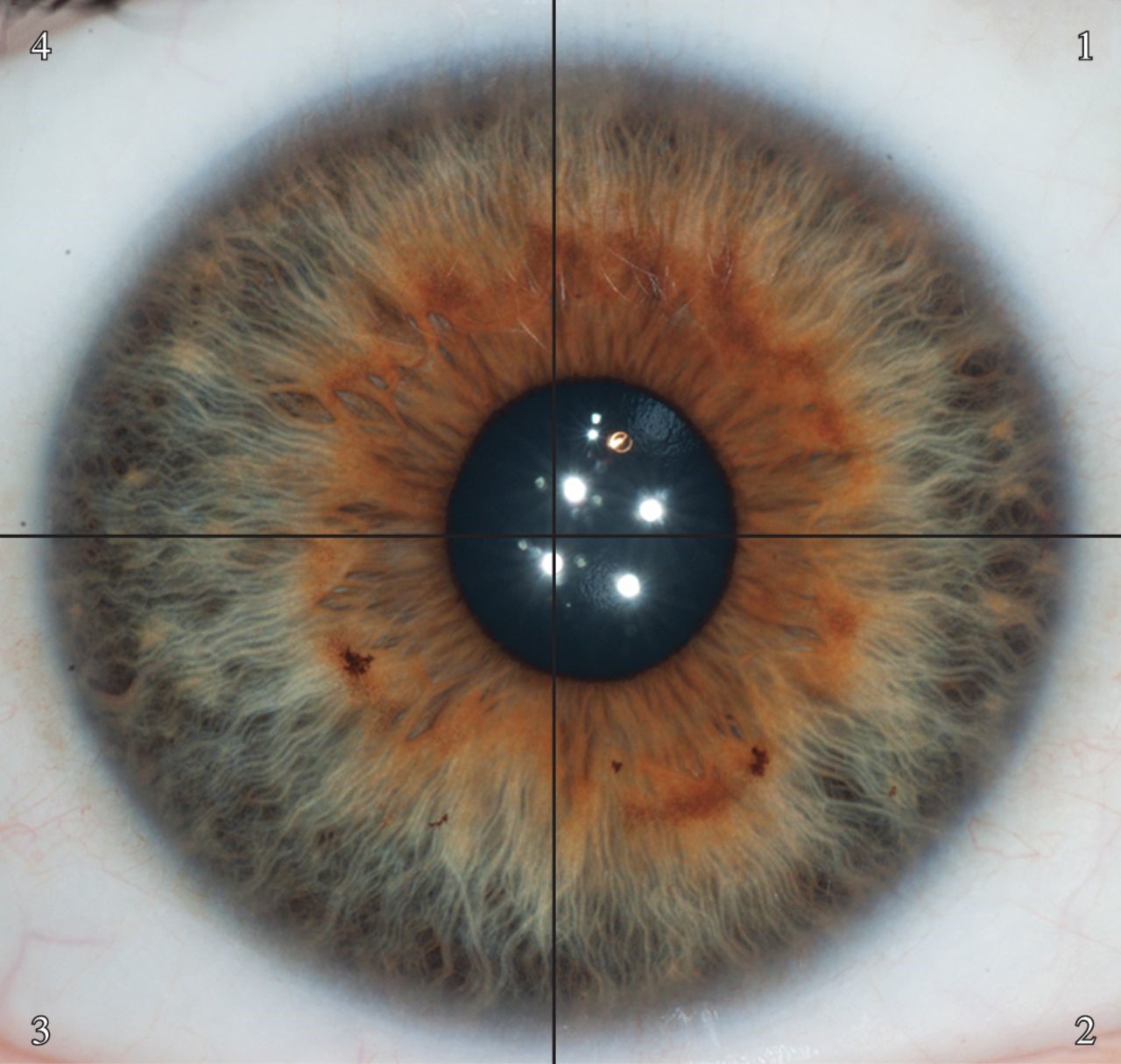
The unique features that are captured from the iris are the mathematical vector-based orientations of the furrows, freckles, and other spots that are contained within it, as illustrated below:
In terms of actually being embedded into a device, it is Fingerprint Recognition that is used the most.
In these instances, probably the most popular example of this is the “Touch ID” system, that is already implemented into the various mobile phones, as illustrated below:

Conclusion
Our next blog post of the series will examine the concept of Two Factor Authentication – 2FA, and how Biometrics can be used there as well, either as the primary layer or the secondary layer of security.